Similar Posts
Installing VS Code on Arch Linux Takes Some Thinking
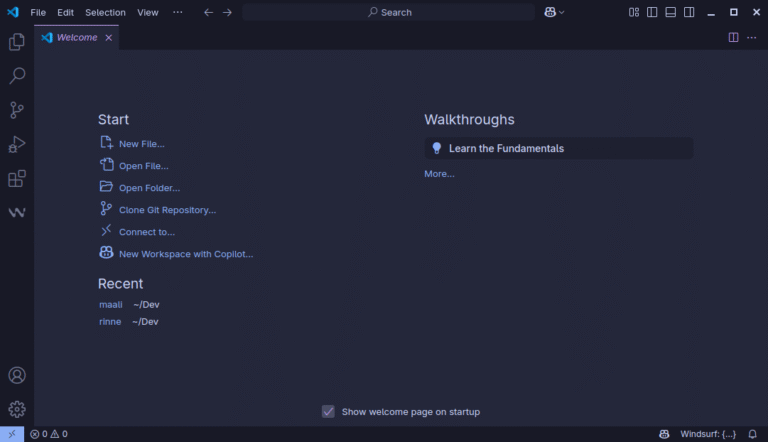
There are two main choices for getting VS Code on Arch Linux: Install Code – OSS…

The First Rust CVE in Linux Kernel Only Makes Your System Crash
So what happened is, CVE-2025-68260 affects the Android Binder driver, which was rewritten in Rust for…

How to Make Every Click Count with Search Experience Optimization
If you’re adopting an SXO approach, you need to focus on metrics that truly reflect user…


Enhancing Search Functionality with Astro Actions and Fuse.js
### Enhancing Search with Astro Actions and Fuse.js Static websites are fantastic, and I’m a huge…

Set an AppImage Application as Default App
Imagine you found a cool text editor like Pulsar and downloaded it in the AppImage format….